Technology is a high-paced thing, and companies are under pressure to keep up with it. Legacy Modernization has come to be a serious agenda among companies that currently use the old systems to conduct their daily operations. You may find that the performance is slowing down, maintenance costs are increasing, and security threats are increasing yearly. All these problems cause tension amongst teams and restrict innovation. Then, what actually happens when the old systems are retarding progress? And how do companies get back in control without derailing the fundamental processes?
Meanwhile, leaders desire systems that can enable development, flexibility, and more intelligent decision-making. Their goals are to enhance performance besides safeguarding the vital data and business logic. Such an equilibrium needs a good technical direction and strategy. Thus, it is critical to comprehend the acceptable strategy to achieve success in the long term. This blog will discuss all the major points of legacy modernization step by step.
Ready to move beyond outdated systems that slow down your business? Mindpath offers legacy modernization services to help you upgrade and transform legacy applications into scalable and future-ready solutions.
What is Legacy Modernization?
Legacy modernization involves updating old software and infrastructure to new modern technologies and architectures. It enhances the performance, security and scalability without altering the underlying business logic. Businesses rely on it in order to remain competitive and promote growth. This strategy enhances the current systems and makes them ready to meet the current digital requirements without necessarily interfering with day to day activities.
However, legacy system modernization goes beyond technical upgrades. Companies need to reconsider procedures, user experience and long term objectives. They enhance efficiency, mitigate risk and facilitate innovativeness with strategic change. An effective modernization strategy puts technology into business performance and establishes a platform to achieve the long-term digital development.
Why is Legacy Modernization Important?
Outdated systems slow progress and increase risk. The modernization of legacy applications helps businesses improve performance, security, and flexibility. Here are some of its key benefits:
1. Legacy modernization reduces high maintenance and infrastructure costs. It also reduces the reliance on the old systems and costly specialists support.
2. It enhances the rate of speed and general dependability of the system. Teams are also able to update at a higher pace and handle changes with ease.
3. It enhances security because it eliminates the risks associated with outdated software. Organizations remain updated on new compliance standards and regulations as well.
4. It improves agility and promotes inter-team innovation. Companies are able to introduce new functionality in a shorter time and react to the needs of the market.
5. Contemporary systems can easily manage increasing traffic and information. They are also compatible with cloud computing and other sophisticated analytics solutions.
6. It improves user experience by making the user interfaces and performance cleaner. There is a greater work efficiency and confidence among the employees when using the system.
How to Modernize Legacy Applications?
Organizations must take a clear and strategic approach to legacy modernization to avoid disruption and control risk. A structured plan helps teams upgrade systems efficiently while supporting business goals and future growth.
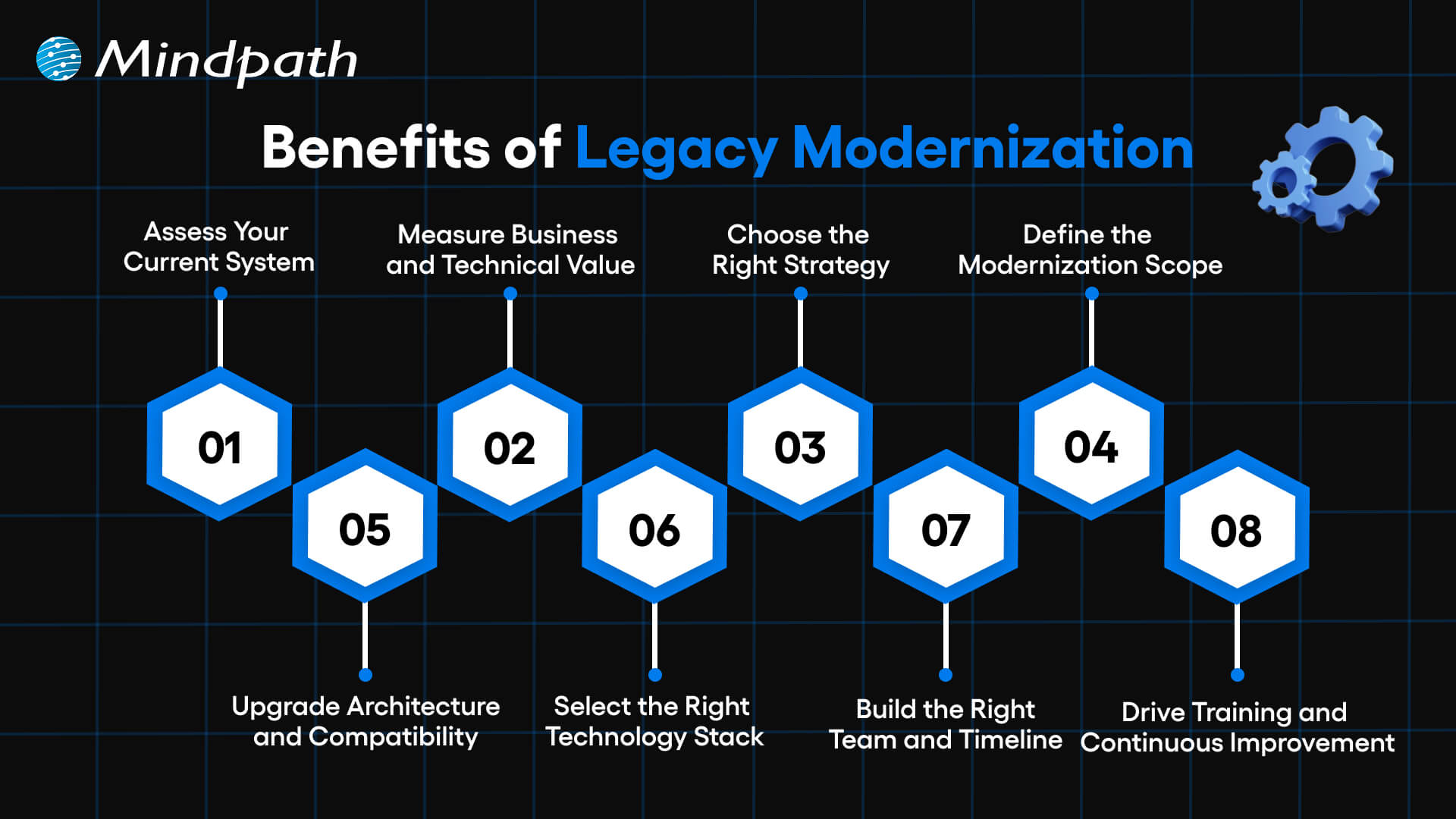
1. Assess Your Current System
Evaluate your applications both business and IT. Determine deficiencies in performance, security and scalability. This step builds a strong base for legacy modernization decisions.
2. Measure Business and Technical Value
Assess business fit, agility, cost, complexity and risk. Know the amount of value each system brings in the present day. Clear insights strengthen your legacy app modernization strategy.
3. Choose the Right Strategy
Select a legacy modernization approach that aligns with business goals. Compare such options as rehost, refactor, rebuild or replace. Take the course of action that brings more quickly and reduces the risk.
4. Define the Modernization Scope
Target key points that lead to business performance. Eliminate the old and unwanted functions that complicate things. A clear scope helps teams modernize legacy applications with confidence.
5. Upgrade Architecture and Compatibility
Use scalable architecture when needed e.g. microservices. Enhance dynamism and streamline administration of the system. Enhance seamless integration with other tools/ platforms.
6. Select the Right Technology Stack
Select technologies that will be able to accommodate existing needs and expand in the future. Never act on your judgment without consulting experts. Good testing will guarantee effectiveness, protection and dependability.
7. Build the Right Team and Timeline
Create a cross functional team with established responsibilities and ownership. Develop and maintain documentation. Set realistic milestones to guide legacy modernization progress.
8. Drive Training and Continuous Improvement
Train the staff on effective use of the new system. Onboarding is encouraged by means of structured support. Continuous updates keep legacy modernization relevant and sustainable.
Key Challenges in Legacy Modernization
There are some valid advantages of legacy modernization, but it also possesses actual challenges. During the transition, organizations have to be ready to overcome technical, financial, and operational challenges.
1. Complex Legacy Code
Systems are difficult to comprehend and expand due to old-fashioned code and lack of documentation. Such complexity slows the development and raises its maintenance costs.
2. Integration Barriers
The old systems also fail to make connections with cloud providers and new APIs. Architecture reengineering will require teams to be mindful of downtime and the gaps in security.
3. Security and Compliance Gaps
The existing security and regulations are not met in aging systems. It is necessary that Legacy Modernization involves proactive protocols, encryption, and compliance control updates.
4. High Costs and Limited Resources
Modernization demands investment in equipments, education, and infrastructures. Lack of a proper roadmap will increase costs and strain internal resources.
5. User Resistance to Change
Employees tend to be at ease with the well-known systems. Good communication, training will enable teams to adjust to Legacy Modernization programs.
6. Performance and Scalability Limits
Old applications are unsuitable to meet the increasing data and user requirements. Legacy Modernization enhances speed, stability, as well as long term scalability.
7. Knowledge and Skill Gaps
It may be challenging to locate professionals with knowledge of old technologies. Lack of experience will put risks and time delays at a higher level and make the project more complex.
8. Data Migration Risks
Migration of mass volumes of old data can result in loss, corruption or compatibility problems. There has to be audits, backups and testing of data to ensure data integrity in Legacy Modernization.
8 Legacy Modernization Strategies for Modern Businesses
Companies must have a strategy in place when modernizing old systems. The right legacy modernization strategies assist in decreasing risk and faster business worth.
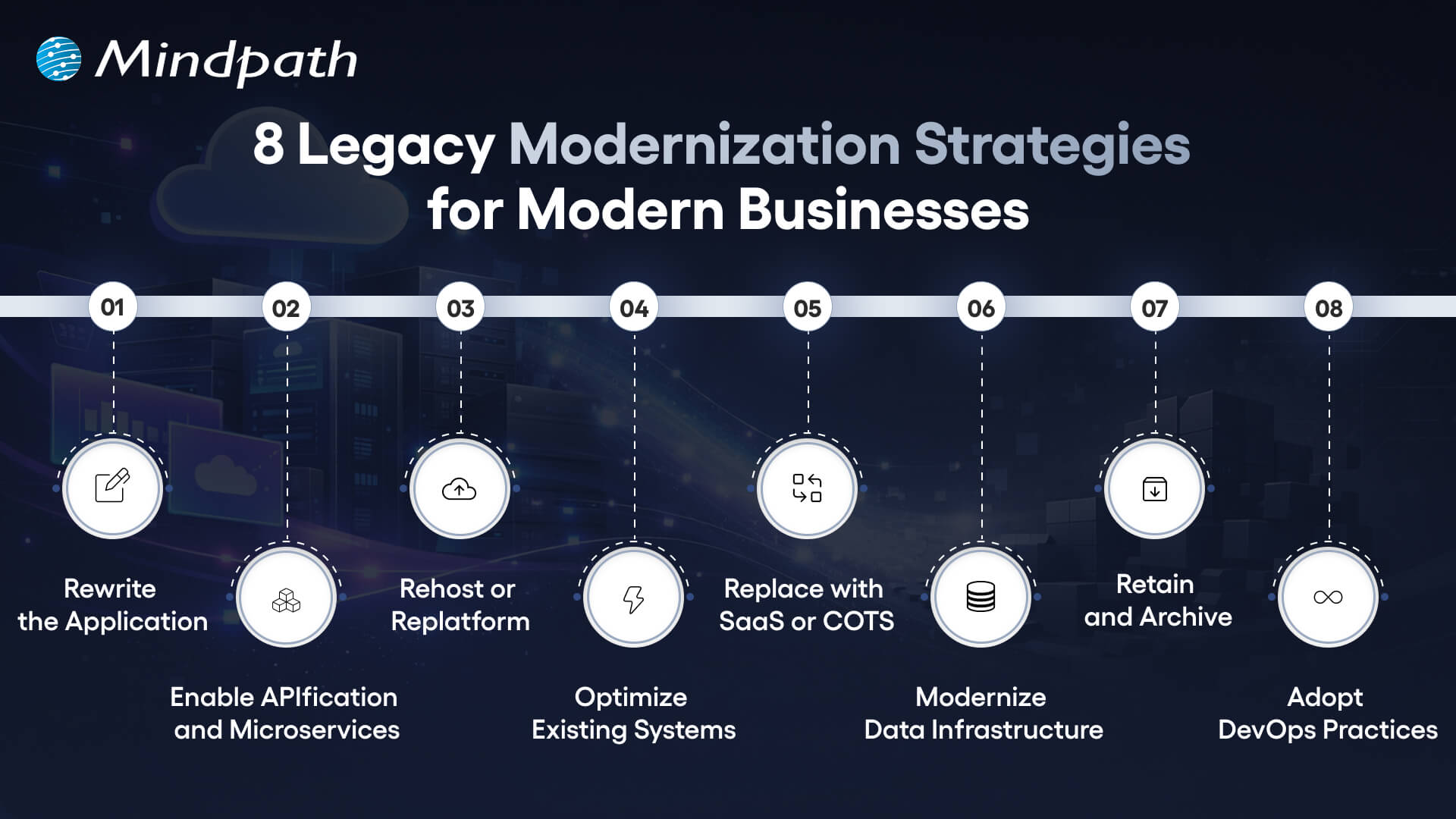
1. Rewrite the Application
Rewrite the old systems using new languages. This strategy will modernize the application and enhance quicker updates. It also reduces the long term maintenance.
2. Enable APIfication and Microservices
Divide monolithic systems into small services. APIs can be used to better integrate them. Innovation is accelerated through this model.
3. Rehost or Replat form
Migration to the cloud with minimal code modification. It is a move that minimizes infrastructure expenses within a very short time. The teams enhance scalability without causing much disturbance.
4. Optimize Existing Systems
Check the workloads as well as code performance gaps. Minimize the usage of infrastructure and operations expenditures. Utilize savings to finance additional upgrades.
5. Replace with SaaS or COTS
Use pre-made platforms that will satisfy business requirements. Accomplish security and compliance. Implement solutions in a shorter time and with reduced risk.
6. Modernize Data Infrastructure
Move the old databases to scaled systems. Enhance the speed, analytics, and flexibility. This step should be aligned to Legacy Modernization.
7. Retain and Archive
Retain those systems that retain the necessary value. Audits of applications that are rarely used in the archive. Unnecessary changes and risks should be avoided.
8. Adopt DevOps Practices
Implement continuous integration and testing. Publishing is faster and teamwork becomes better. Enhance the performance and stability of the systems.
Key Trends for Legacy Modernization System
Organizations are still redefining their technology environment to remain competitive. The modernization trends point to the new directions that lead to faster, smarter and more scalable transformation.
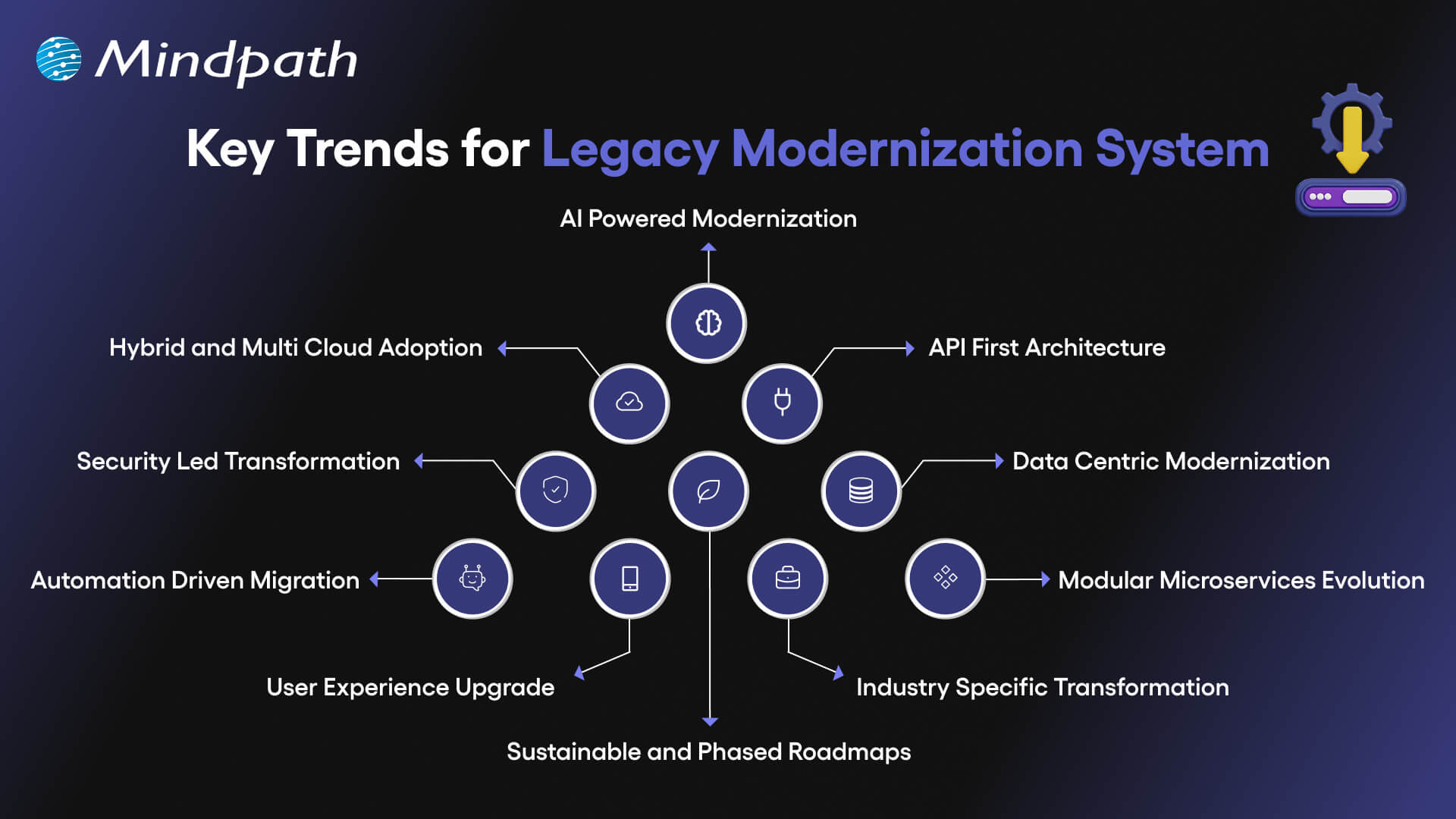
1. AI Powered Modernization
Code refactoring, re-architecture and system analysis are now assisted by AI. According to legacy modernization trends, many enterprises spend lots of money in AI. It enhances preciseness, less threat, and accelerates change.
2. Hybrid and Multi Cloud Adoption
Organizations have stopped relying on one cloud provider. They operate hybrid and multi cloud environments to be flexible and resilient. Container platforms assist systems to operate efficiently in environments.
3. API First Architecture
Enterprises substitute monolithic models with modular API based models. The APIs enhance integrations, scalability, and expedited feature upgrade. The change holds its ground in the contemporary legacy modernization patterns.
4. Security Led Transformation
The presence of stringent rules encourages companies to advance the old security checks. Zero trust models, encryption, and enhanced access management are implemented in teams. Every modernization roadmap is currently being influenced by security.
5. Data Centric Modernization
Isolated data warehouses are sent to unified lake house platforms by businesses. This measure enhances real-time understanding and information controls. Powerful data strategy is a key to successful legacy software modernization.
6. Automation Driven Migration
Code scanning, risk detection, and recommendation are processes performed by AI-based tools. Jurisdictional testing and documentation lowers the manual work involved. These applications reduce migration time.
7. Modular Microservices Evolution
Businesses upgrade microservices using containers and orchestration technology. AI assists in tracking and optimization of working loads. This will enhance system stability and scalability.
8. User Experience Upgrade
The future UX concentrates on customization, usability, and functionality. Component based design models substitute strict legacy interfaces. These enhancements are in line with wider patterns of legacy modernization.
9. Industry Specific Transformation
Banks, healthcare providers, and manufacturers need individual solutions. Modern systems are now able to comply with strict industry rules. A strong legacy modernization framework supports niche requirements effectively.
10. Sustainable and Phased Roadmaps
Companies are ready to upgrade slowly than to rewrite everything. Planned phase will guarantee the sustainability of long term and reduce disruption. This approach makes modernization anticipative and expandable.
Examples of Legacy Systems
Several organizations are still using the old systems to execute important activities. These are the legacy systems that are still in use and support day-to-day processes in spite of low adaptability and scalability.
1. Cloud Enablement in Financial Services
To enhance scaling and reporting, a fintech company has transferred the core systems to the cloud. This legacy modernization decreased manual labor and increased reliability.
2. Clinical Platform Enhancement
A microservices-based upgrade of an oncology system to speed up its performance. The transformations enhanced integration and helped to make medical decisions faster.
3. High-Performance Trading Systems
Microservices and automated deployments were embraced in a trading platform. This legacy modernization enabled speed and increased volume of transactions.
4. Digital Leasing Transformation
One leasing system upgraded its infrastructure to initiate operations more quickly. The upgrade made the operations less complex and efficient.
5. Smart Assessment Innovation
One of the education platforms presented AI-based grading tools. The educators used to save some time and received more rapid performance feedback.
6. Scalable K-12 Learning Infrastructure
One school system optimized its cloud environment to its maximum. The upgrade also enhanced the uptime and made the learning process stable.
Ready to Future Proof Your Business?
Legacy systems limit growth, increase risk, and slow innovation. Organizations that invest in legacy modernization improve performance, security, and scalability while reducing long term costs. A clear strategy helps teams modernize in phases and avoid disruption. With the right approach, businesses build flexible systems that support innovation, improve user experience, and create lasting competitive advantage in a fast changing digital market.
Mindpath stands as a trusted legacy modernization service provider delivering practical and scalable solutions. Our team assesses existing systems, defines a clear roadmap, and executes modernization with minimal disruption. We focus on performance, security, and cloud readiness to create measurable business value. With proven expertise and strong technology partnerships, Mindpath helps enterprises modernize confidently and achieve sustainable digital growth.
FAQs
1. What is Legacy Modernization and why should my business consider it now?
Legacy modernization helps businesses upgrade aging systems to improve speed, security, and scalability. Companies adopt it to reduce operational risks and support innovation. When technology limits growth, modernization creates a strong digital foundation. It also prepares organizations to integrate cloud, data analytics, and automation effectively.
2. How do I know if my organization needs legacy modernization?
Frequent system failures, high maintenance costs, and slow feature releases signal deeper issues. If your teams struggle to scale or integrate modern tools, your systems likely restrict progress. Legacy modernization helps you overcome these limits and align technology with current business goals and customer expectations.
3. How can Mindpath support our modernization journey?
Mindpath’s legacy modernization services focus on strategy, assessment, and execution with minimal disruption. Our experts analyze your systems, design a practical roadmap, and implement scalable solutions. As a trusted legacy modernization company, Mindpath ensures measurable performance gains and long-term technology stability.
4. What technical approaches work best for modernizing complex legacy systems?
The right approach depends on architecture, dependencies, and business priorities. Teams may rehost applications in the cloud, refactor code into microservices, or rebuild critical components. A structured legacy modernization plan ensures integration stability, secure data migration, and improved system performance.
5. How do we manage risk during legacy application transformation?
Teams reduce risk through phased execution, automated testing, and strong DevOps practices. Clear documentation and system audits help identify hidden dependencies early. Mindpath’s legacy modernization services follow controlled deployment models that protect data integrity and maintain operational continuity throughout the transition.












